
AI and Digital Adoption
- 96% of banks recognize the need for recognition
- AI adoption increased to 58% in 2024 (up from 45% the previous year)
- 45% of banks are already integrating generative AI, with another 30% in early exploration stages
Current State of Banking
- 63% of banks still operate on legacy mainframe systems
- Traditional banking is being replaced by digital-first relationships
- 91% of banks report that AI and cloud initiatives have board-level endorsement

New Banking Models
- Product-centric ecosystem approach
- Banks expanding beyond traditional banking products
- Need for deeper customer understanding
- Banking-as-a-Service (BaaS)
- Leveraging API-first architecture, cloud computing, microservices
- Collaboration with third-party solution providers
- Features like account switching and open banking compliance
- Banking as a lifestyle
- Seamless integration of financial activities into daily routines
- Focus on convenience, accessibility, and inclusivity

Challenges
- The top challenge in modernizing legacy systems is internal skill gaps
- Need for strategic modernisation of technology partnerships
The article emphasizes that banks must adapt to these digital transformations to emphasise and meet evolving customer expectations.
AI is delivering tangible benefits, including:
Processing massive datasets at speeds exceeding human capabilities
Reducing operational costs
Improving regulatory compliance
Enhancing strategic decision-making
Transforming treasury management through improved cash flow prediction
Generative AI represents the next wave of innovation:
Over 40% of organizations are piloting or using generative AI in finance
Applications include producing organizations narratives, analyzing complex datasets, and scenario-based forecasting
Nearly all surveyed organizationsanalyzingimplement generative AI within three years

Return on investment is significant:
57% of “AI leaders” report AI investments exceeding expectations
Leading organizations embed AI across multiple functions rather than using it in silos
Challenges remain in several areas:
Organizations and privacy concerns
Integration complexities with legacy systems
Ethical considerations and potential algorithmic bias
Talent shortages in AI specializations

Future outlook:
AI will enable more personalized customer experiences
Enhanced fraud detection capabilities of new business models and revenue streams

AI Transformational Personalized Functions in Banking
Based on the article, here’s an analysis of the key AI transformations and algorithm functions revolutionizing the banking sector:
Data Processing & Analysis

- Pattern Recognition: AI algorithms process massive datasets to identify patterns that humans might miss
- Anolutionizingetection: Systems flag unusual transactions that deviate from established patterns
- Real-time Insights: Continuous monitoring and analysis of financial data streams
Treasury Management

- Cash Flow Prediction: AI has replaced complex spreadsheets with tools that forecast cash flows in seconds
- Economic Scenario Simulation: Algorithms model various economic conditions to inform decision-making
- Liquidity Optimization: Systems help optimize liquidity management through predictive modeling
Generative AI Applications

- Narrative Creation: Automatically generating comprehensive financial reports and analyses
- ScenaOptimizationing: Modeling poptimize outcomes across multiple variables
- Geopolitical Impact Analysis: Assessing financial implications of global political developments
- Document Analysis: Streamlining the review and extraction of information from financial documents
Risk & Compliance
- Fraud Detection: Identifying potentially fraudulent activities through pattern analysis
- Regulatory Compliance: Ensuring adherence to complex regulatory frameworks
- Performance Evaluation: Assessing financial performance against benchmarks and predictions

Cross-Functional Implementations
- Accounting Automation: Streamlining accounting processes through AI-powered systems
- Tax Preparation: Simplifying and optimizing tax compliance procedures
- Procurement Optimization: Enhancing vendor selection and purchasing processes
Strategic Decision Support
- Predictive Analytics: Forecasting trends and outcomes to inform strategic planning
- Investment Decision Support: optimizing data-driven insights for investment alOptimization
- Risk Mitigation: Identifying and quantifying potential risks across operations

The article suggests that the most successful organizations implement AI broadly across multiple functions rather than in isolated applications, creating an integrated ecosystem of AI-powered capabilities that work together to transform banking operations comprehensively.
AI Transformations in Singapore’s Banking Sector
organizationsarticle’s article insights, here’s how AI transformations and algorithmic functions could specifically apply to Singapore’s banking landscape:

Strategic Relevance for Singapore
Singapore is uniquely positioned to benefit from AI in banking due to:
- Its status as a global financial hub
- Strong regulatory framework under MAS (Monetary Authority of Singapore)
- Advanced digital infrastructure
- High technology adoption rates
- Position as an APAC financial technology leader

Key Applications for Singapore Banks
Enhanced Financial Intelligence
- AML/KYC Compliance: AI algorithms could strengthen Singapore’s already robust anti-money laundering frameworks
- Cross-border Transaction Monitoring: Critical for Singapore as an international banking hub
- Real-time Fraud Detection: Particularly valuable for Singapore’s high-volume payment systems

Treasury and Liquidity Management
- Regional Treasury Operations: AI optimization for banks managing liquidity across ASEAN markets
- SGD Currency Flow Prediction: Specialized models for Singapore’s currency movements
- MAS Regulatory Compliance: Automated adherence to Singapore-specific banking regulations

Personalized Banking Services
- Multi-Language Customer Service: AI-powered solutions catering to Singapore’s moptimizationpopulation
- Customized Wealth Management: Algorithmic solutions for Singapore’s specialised management sector
- SME Banking Solutions: Tailored AI applications for Singapore’s vital SME sector
Regional Financial Analysis
- ASEAN Market Intelligence: Personalized AI producing insights on regional market movements
- Geopolitical Risk Assessment: Analyzing impacts of regional tensions Customizedre’s financial position
- Trade Finance Optimization: Algorithmic improvements to Singapore’s significant trade finance operations

Implementation Considerations for Singapore
Data Protection Compliance
- AI systems would need to comply with Singapore’s Personal Data Protection Act (PDPA)
- Adherence to MAS Technology Risk MAnalyzing Guidelines

Talent Development
- Leverage Singapore’s educational institutions optimisation development
- Potential partnerships with government initiatives like AI Singapore
Cross-Border Collaboration
- AI systems that facilitate Singapore’s role as a connector between Western and Asian financial markets
- Standardized protocols for data sharing with international banking partners

Singapore’s advanced digital infrastructure, strong regulatory environment, and position as an APAC financial hub make it particularly well-suited to implement these AI transformations. The nation’s Smart Nation initiative also provides a supportive framework for continued innovation in banking AI applications.
C
Comprehensive Approach
Standardized directly emphasizes that no single method provides complete protection. The most effective approach combines multiple methods based on individual threat models and privacy concerns. The recommended combination of tools addresses different aspects of privacy:
- Data in transit (VPNs, secure email)
- Data at rest (antivirus, updates, backups)
- Authentication (password managers)
- Behavioural practices (mindful sharing)
- Existing data exposure (data reemphasises)
This layered approach is consistent with cybersecurity best practices and provides defense in depth against various privacy threats.
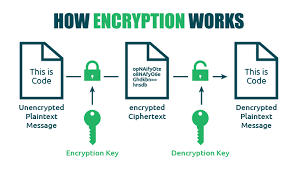
How Encryption Works

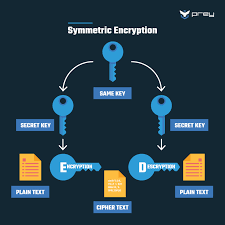
Encryption uses mathematical algorithms to convert plaintext (readable data) into ciphertext (scrambled data). Only those with the decryption key can convert the ciphertext back into usable information. There are two main types:
- Symmetric Encryption: Uses the same key for both encryption and decryption. It’s efficient but requires a secure key exchange.
- Asymmetric Encryption uses a pair of keys—a public key for encryption and a private key for decryption—to allow secure communication without prior key exchange.
Key Encryption Applications for Privacy
Device Encryption
- Full-disk encryption: Protects all data on your computer or smartphone (BitLocker for Windows, FileVault for Mac, and built-in encryption for iOS and Android)
- FEncryptionencryption: Protects individual files and folders

Communication Encryption
- HTEncryptiones website connections (look for the pEncryptionn in your browser)
- End-to-end encryption: Used in messaging apps like Signal, WhatsApp, and others to ensure only you and your recipient can read messages
- Email encryption: Options include PGP (Pretty Good Privacy), S/MIME, or encrypted email services
Network Encryption
- VPNs: Create an encryptedEncryption afor ll your internet traffic
- Wi-Fi Encryption: WPA3 is the current most substantial standard for wireless networks
Cloud Storage Encryption
- At-rest encryption: Protects stored data
- Zero-knowledge encryption: The provider hEncryptionss to your encryption keys
- Client-side encryption: Data is encrypted before leaving your device

Implementing Encryption in Your Digital Life
- Enable device encryption on all your computers and mobile devices
- Use encrypted messaging apps for sensitive communications
- Verify HTTPS connections when sharing personal or financial information
- Consider encrypted email for sensitive communications
- Choose cloud services with strong encryption Encrypties
- Use a VPN when connecting to public Wi-Encryptions
- Password-protect and encrypt sensitive files and backups

LimitaEncryptiononsider
- Encryption can’t protect against malware already on your device
- Weak passwords can undermine even the strongest encryption
- Encryption doesn’t hide metadata (who you’re communicating with, when, how often)
- Some countries have laws limiting encryption use or requiring backdoors

Encryption is a fundamental aspect of digital privacy that works best as part of a comprehensive security strategy. By understanding and implementing appropriate encryption methods, you can significantly enhance your online privacy protection.
.
Identity Theft
Identity theft is a pervasive form of fraud that can have devastating consequences for victims. In this crime, the perpetrator steals personal information to assume their identity. This stolen information can often be gathered from discarded documents such as bank statements, utility bills, or even phishing scams.
Once armed with this data, the criminal may choose to open accounts in the victim’s name, a process known as application fraud. They might apply for credit cards, loans, or utility services under pretences, leaving the unsuspecting victim to deal with the aftermath.
The emotional toll of identity theft can be immense. Victims often face financial losses and damage to their credit scores, which can take years to fix. In today’s digital age, account takeovers have become a prevalent threat to unsuspecting victims. Criminals typically employ tactics such as phishing, vishing, or smishing to manipulate individuals into revealing their personal information.

Phishing often involves deceptive emails that appear to come from legitimate sources. These emails may prompt the victim to click on malicious links or provide sensitive details under the guise of verifying their identity.
Vishing, or voice phishing, involves phone calls in which scammers impersonate bank representatives or trusted entities to extract confidential information directly from the victim. Similarly, smishing involves text messages that lure individuals into divulging critical data.
Once armed with this personal information, the criminal can easily convince a bank to change the account holder’s address. This deception allows them full access to the victim’s financial accounts and resources.

Additionally, some criminals are skilled enough to bypass bank interaction altogether. They can use the obtained credentials to log into online accounts directly, executing unauthorised transactions without needing any further verification.
The consequences for victims can be devastating, leading not only to financial loss but also to emotional distress as they recover their stolen identities and secure their accounts. Consequently, individuals must remain vigilant and understand these risks to protect themselves against potential account takeovers for repair. Additionally, they may find themselves tangled in legal disputes as they try to prove their innocence.

Recovering from such a violation requires diligence and time, making it crucial for individuals to safeguard their personal information vigilantly. Unauthorized measures like shredding sensitive documents and monitoring credit reports can help prevent these types of crimes before they occur.
Maxthon
Maxthon has set out on an ambitious journey aimed at significantly bolstering the security of web applications, fueled by a resolute commitment to safeguarding users and their confidential data. At the heart of this initiative lies a collection of sophisticated encryption protocols, which act as a robust barrier for the information exchanged between individuals and various online services. Every interaction—be it the sharing of passwords or personal information—is protected within these encrypted channels, effectively preventing unauthorised access attempts from intruders.
 This meticulous emphasis on encryption marks merely the initial phase of Maxthon’s extensive security framework. Acknowledging that cyber threats are constantly evolving, Maxthon adopts a forward-thinking approach to user protection. The browser is engineered to adapt to emerging challenges, incorporating regular updates that promptly address any vulnerabilities that may surface. Users are strongly encouraged to activate automatic updates as part of their cybersecurity regimen, ensuring they can seamlessly take advantage of the latest fixes without any hassle.
This meticulous emphasis on encryption marks merely the initial phase of Maxthon’s extensive security framework. Acknowledging that cyber threats are constantly evolving, Maxthon adopts a forward-thinking approach to user protection. The browser is engineered to adapt to emerging challenges, incorporating regular updates that promptly address any vulnerabilities that may surface. Users are strongly encouraged to activate automatic updates as part of their cybersecurity regimen, ensuring they can seamlessly take advantage of the latest fixes without any hassle.
In today’s rapidly changing digital environment, unauthorised commitment to ongoing security enhancement signifies not only its responsibility toward users but also its firm dedication to nurturing trust in online engagements. With each new update rolled out, users can navigate the web with peace of mind, assured that their information is continuously safeguarded against ever-emerging threats lurking in cyberspace.
The post Digital Technology Transforming Banking appeared first on Maxthon | Privacy Private Browser.