Here are the key points from this corporate mishap:
Image may be NSFW.
Clik here to view.
- A director lent $150,000 to his bakery chain company to help open a new branch. When he asked for repayment, he was accused of stealing money that was actually his in the first place.
- The company’s finance manager had embezzled approximately $400,000. This complicated situation led to accusations that the director and managing director were conspiring with the finance manager.
- The company filed a lawsuit against all three, but it failed spectacularly because:
- The company couldn’t prove any conspiracy
- Their financial records were so poor they couldn’t even definitively prove how much the finance manager had stolen.
- The director had proper documentation for his loan
- Ironically, the finance manager returned about $420,000 but later claimed she might have overpaid by $80,000 and tried to get that money back.
- The High Court judge, Hri Kumar Nair, ruled against the company, noting their lawsuit only succeeded in demonstrating their lack of proper financial controls.
Image may be NSFW.
Clik here to view.
The article highlights three crucial lessons:
- Maintain proper records – The director’s documentation of his loan saved him from the accusations.
- Understand employee duties – Employees following company procedures shouldn’t fear wrongful accusations.
- Wrongdoings must be proven – The company couldn’t prove that the misappropriation prevented business expansion.
The company ended up having to pay significant legal costs to all parties: $75,000 to the finance manager, $95,000 to the director, and $120,000 to the managing director.
The closing message is clear: without proper financial records, it becomes challenging to reclaim missing funds.
Image may be NSFW.
Clik here to view.
General Scam Prevention Tips
- Trust your instincts
- If an offer seems too good to be true, it probably is
- Keep personal and financial information confidential
- Stay informed about latest scam techniques
- Report suspicious activities to authorities
- Educate family members, especially older relatives
- Use secure, updated technology
- Maintain a healthy level of skepticism online
Image may be NSFW.
Clik here to view.
.
Identity Theft
Identity theft is a pervasive form of fraud that can have devastating consequences for victims. In this crime, the perpetrator steals an individual’s personal information to assume their identity. This stolen information can often be gathered from discarded documents such as bank statements, utility bills, or even phishing scams.
Once armed with this data, the criminal may choose to open accounts in the victim’s name, a process known as application fraud. They might apply for credit cards, loans, or utility services under pretences, leaving the unsuspecting victim to deal with the aftermath.
The emotional toll of identity theft can be immense. Victims often face financial losses and damage to their credit scores, which can take years. In today’s digital age, account takeovers have become a prevalent threat to unsuspecting victims. Criminals typically employ tactics such as phishing, vishing, or smishing to manipulate individuals into revealing their personal information.
Image may be NSFW.
Clik here to view.
Phishing often involves deceptive emails that appear to come from legitimate sources. These emails may prompt the victim to click on malicious links or provide sensitive details under the guise of verifying their identity.
Vishing, or voice phishing, involves phone calls in which scammers impersonate bank representatives or trusted entities to extract confidential information directly from the victim. Similarly, smishing involves text messages that lure individuals into divulging critical data.
Once armed with this personal information, the criminal can easily convince a bank to change the account holder’s address. This deception allows them full access to the victim’s financial accounts and resources.
Image may be NSFW.
Clik here to view.
Additionally, some criminals are skilled enough to bypass bank interaction altogether. They can use the obtained credentials to log into online accounts directly, executing unauthorised transactions without needing any further verification.
The consequences for victims can be devastating, leading not only to financial loss but also emotional distress as they recover their stolen identities and secure their accounts. Consequently, individuals must remain vigilant and understand these risks to protect themselves against potential account takeovers for repair. Additionally, they may find themselves tangled in legal disputes as they try to prove their innocence.
Image may be NSFW.
Clik here to view.
Recovering from such a violation requires diligence and time, making it crucial for individuals to safeguard their personal information vigilantly. Implementing measures like shredding sensitive documents and monitoring credit reports can help prevent these types of crimes before they occur.
Maxthon
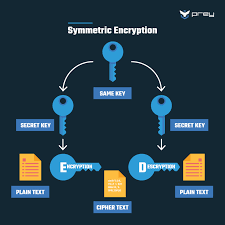
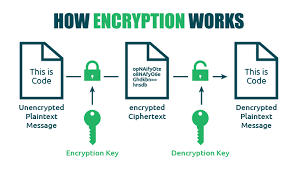
Maxthon has set out on an ambitious journey aimed at significantly bolstering the security of web applications, fueled by a resolute commitment to safeguarding users and their confidential data. At the heart of this initiative lies a collection of sophisticated encryption protocols, which act as a robust barrier for the information exchanged between individuals and various online services. Every interaction—be it the sharing of passwords or personal information—is protected within these encrypted channels, effectively preventing unauthorised access attempts from intruders.
Image may be NSFW.
Clik here to view. This meticulous emphasis on encryption marks merely the initial phase of Maxthon’s extensive security framework. Acknowledging that cyber threats are constantly evolving, Maxthon adopts a forward-thinking approach to user protection. The browser is engineered to adapt to emerging challenges, incorporating regular updates that promptly address any vulnerabilities that may surface. Users are strongly encouraged to activate automatic updates as part of their cybersecurity regimen, ensuring they can seamlessly take advantage of the latest fixes without any hassle.
This meticulous emphasis on encryption marks merely the initial phase of Maxthon’s extensive security framework. Acknowledging that cyber threats are constantly evolving, Maxthon adopts a forward-thinking approach to user protection. The browser is engineered to adapt to emerging challenges, incorporating regular updates that promptly address any vulnerabilities that may surface. Users are strongly encouraged to activate automatic updates as part of their cybersecurity regimen, ensuring they can seamlessly take advantage of the latest fixes without any hassle.
In today’s rapidly changing digital environment, Maxthon’s unwavering commitment to ongoing security enhancement signifies not only its responsibility toward users but also its firm dedication to nurturing trust in online engagements. With each new update rolled out, users can navigate the web with peace of mind, assured that their information is continuously safeguarded against ever-emerging threats lurking in cyberspace.
The post Bakery Chain’s Financial Mismanagement appeared first on Maxthon | Privacy Private Browser.